About our services and security

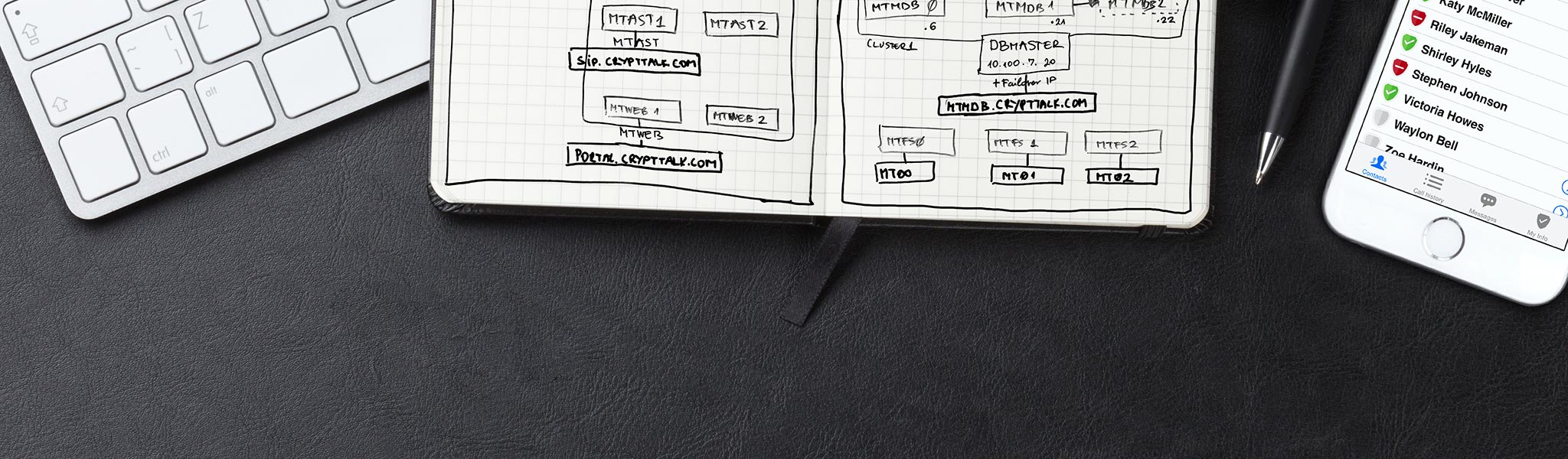
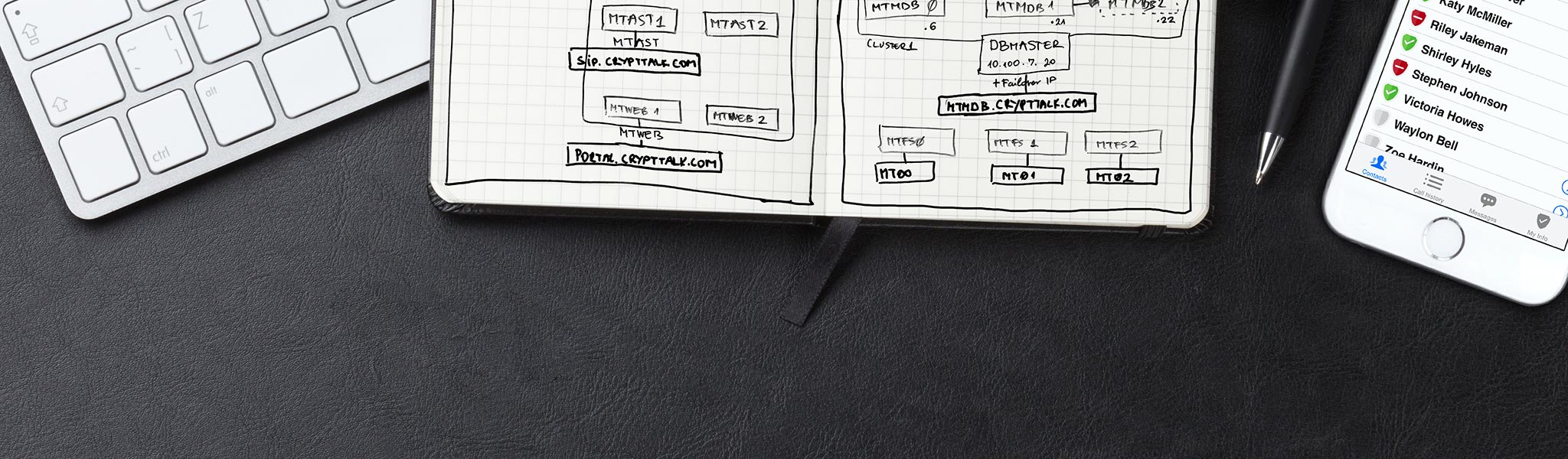
Why trust CryptTalk?
Our security philosophy
Learn more about our
security philosophy.
Our security philosophy

CryptTalk Security
White Paper
Discover how CryptTalk makes your communication completely secure.
Download White Paper (PDF)

Proven Security
NCC review details
Learn about the CryptTalk Mobile
Application Security Assessment
by NCC Group.
Assessment details

Product
brochure
See CryptTalk's main features.
Open brochure (PDF)

Markets &
Case Studies
See how our customers
from various sectors
benefit from using CryptTalk.
Read Case Studies

Support Center &
Frequently Asked Questions
Got any questions? Go to our Support Center for assistance or to submit a question.
Open Help Center
Press resources and some media coverage

Our Story
Interview with the founders
Szabolcs Kun and Attila Megyeri, co-founders, tell their story.
Read article

Why we do this?
A deeper insight about us
We believe that your personal privacy matters a great deal.
Read article

CryptTalk video spot
(1:30)
A short introduction to CryptTalk.
Watch video

CryptTalk boosted
by encryption controversy
"This is a solution with no back door, without any special hardware
and, very importantly, even we, the vendors,
cannot decrypt calls made using CryptTalk"
Read article

But, aside from the marketing
spiel, how good is CryptTalk?
"Indeed, few companies do not have back doors. CryptTalk, thus, only has two or three competitors in the very secure segment."
Read article

CryptTalk for Journalists
(Interview by GEN)
We are committed to support investigative journalism and the protection of free speech.
Read the interview
For specific inquiries, please email us at: media@crypttalk.com
Reports and articles about surveillance
We have collected you useful articles and reports about surveillance and eavesdropping.

Vodafone outlines government
efforts to censor telecoms
networks
Vodafone Law Enforcement Disclosure
report Country-by-country legal annexe.
Read report

Telenor's report
on
authority requests
Authority requests for access to electronic
communication (country data).
Read report

Bugged, Tracked, Hacked
A 60 Minutes Special Investigation
German hackers intercept and record mobile phone conversations between a 60 Minutes reporter in Europe and an Independent Australian Senator, Nick Xenophon, in Australia's Parliament House.
Watch the report

FORBES on governmental
surveillance
"Statistics on how often your phone company hands data over to law enforcement."
Read article

Keys Under Doormats
(MIT Report)
Mandating insecurity by requiring
government access to all data and
communications.
Read report

Further useful
articles and reports
See our collection of articles
on interception and surveillance.
Coming soon!
For our users

CryptTalk
User's Manual
For individual users subscribing
through the App Store℠.
Open manual

CryptTalk PRO
User's Manual
For business users
with corporate subscription.
Open manual

Privacy
Policy
Open page

Stay secure!
Practical advice
Open page

Legal aspects
of our service
Open page

CryptTalk PRO
Master Service Agreement
Download (PDF)